- QUASAR
- AquaCycle
- Proteins4Singapore
- Singapore's Pathway to Carbon Neutrality
- CellFACE
- LightSPAN
- Computational Modelling Group
- Energy and Power Systems Group
- SITEM - Singapore Integrated Transport and Energy Model
- Past Projects
Events
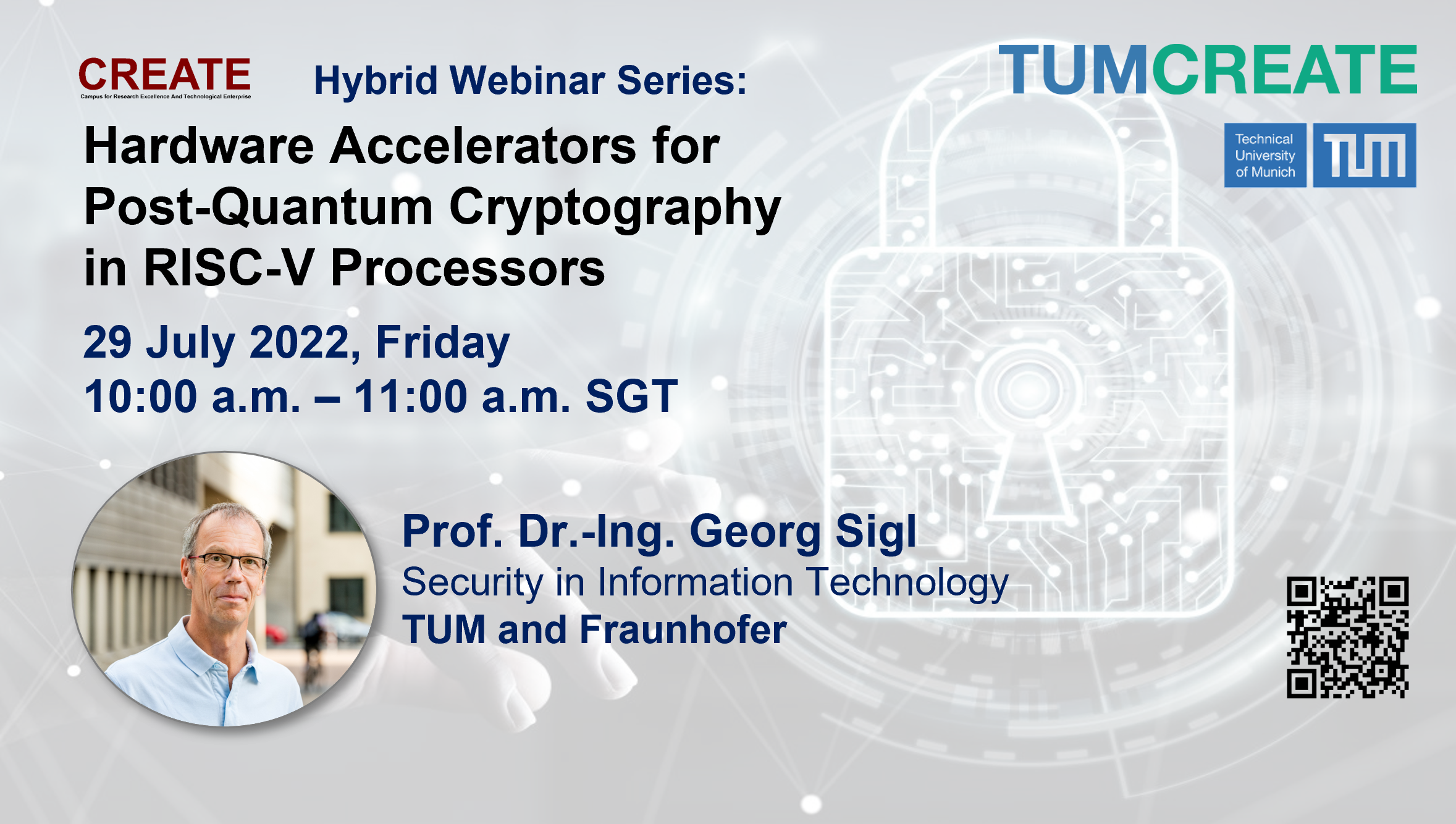
Hardware Accelerators for Post-Quantum Cryptography in RISC-V Processors (A CREATE Webinar Series)
Presented by Prof. Dr.-Ing. Georg Sigl 29.07.2022It's a hybird event!
Join us for an hour with Prof. Dr.-Ing. Georg Sigl, his take on Post-Quantum Cryptography!
Virtual Participation:
https://us06web.zoom.us/j/88145777828?pwd=Q0w1SC9QUS81cm0vanUzSFNLZWtuZz09
Meeting ID: 881 4577 7828
Passcode: 766739In Person Participation:
CREATE Tower, Level 2 Gallery
Singapore 138602Register HERE
Abstract:
In July 2022 the North American standardization organization NIST has announced first winners of their PQC (Post-Quantum Cryptography) competition and announced an extension at the same time. This will initiate a major transition in the cryptographic algorithms used in our daily life over the next years. The talk will start with some background why PQC is needed and about the threats of quantum computers for classical cryptography. After a summary of the results of the NIST competition, the talk will focus on hardware acceleration, which has been accompanying the NIST standardization process. We have contributed to this process tightly coupled accelerators integrated into a RISC-V 32-bit processor, which combine medium performance and power gain with low resource overhead and high flexibility. This enables lattice based PQC schemes even on low cost and low performance microcontrollers. As alternative to lattice based algorithms, SIKE has been proposed as alternate candidate and will be investigated further in the extended competition. Its advantage are short key and message lengths, but it suffers from high computation times. This forces the use of hardware accelerators. The talk presents results of our chip designs in 65nm and gives an outlook at our new design in 22nm.
Biography of Prof. Georg Sigl
Georg Sigl finished his PhD in Electrical Engineering at Technical University Munich in 1992. Afterwards he held several positions in research and development at Siemens and Infineon. From 2000 until 2010 he was responsible for the development of new secure microcontroller platforms in Infineon’s Chip Card and Security division. Under his responsibility, two award winning platforms have been designed. In June 2010, he founded a new chair for Security in Electrical Engineering and Information Technology at Technical University of Munich. In parallel, he is driving embedded security research as director at the Fraunhofer Research Institute for Applied and Integrated Security AISEC Munich. His research interests include cryptographic implementations, side-channel and fault attacks, physical unclonable functions, hardware reverse engineering, and hardware-software security codesign.
Upcoming Events:
No upcoming eventsContact
Corporate Communications TUMCREATE
1 CREATE Way
#10-02 CREATE Tower
Singapore 138602Media and Communications
communications@tum-create.edu.sg

